I Know When You Sleep (Thanks to WhatsApp)

We usually assume that if a messenger app has "End-to-End Encryption" (E2EE), we are invisible. We see the lock icon and think the content is the only thing that matters.
I recently stumbled across a paper by researchers from the University of Vienna titled "Careless Whisper." They demonstrated that while the content of your messages might be locked away, your behavior is being broadcast to anyone who knows your phone number.
The scary part? It requires no malware, no hacking, and the companies behind these apps don't seem interested in fixing it. Excellent.
The Hack: Using Silence to Map Your Life
The vulnerability relies on something unusual: Delivery Receipts.
When a message hits your phone, your device obediently tells the server, "I got it."
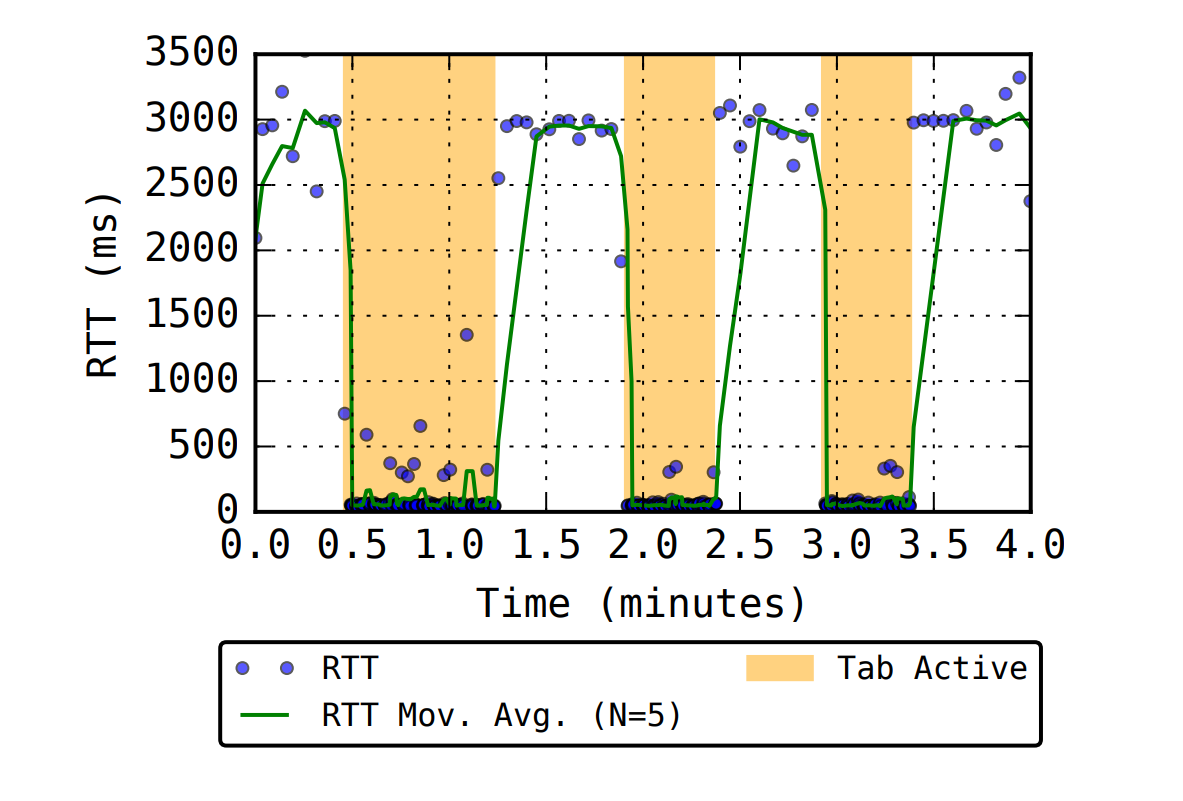
The researchers discovered that the time it takes for your phone to send this receipt (the latency) varies significantly depending on what your phone is doing.
- Screen Off (Standby): Slow response.
- Screen On (Active): Fast response.
- App Open: Instant response.
By sending a stream of invisible messages to a target, an attacker can measure these timings and build a perfect graph of your daily activity. They know when you wake up, when you’re scrolling at work, and when you go to sleep.
What Can They Actually See?
It’s easy to dismiss this as "just knowing when I'm online." But data is never just data; it's context. By simply analyzing the timing of these receipts, an attacker can fingerprint an alarming amount of information:
- Device Type: They can distinguish between different phone makes (iPhones, Samsungs, or Xiaomi) based on processing speeds.
- Connection Status: They can tell if you are on Wi-Fi (predictable latency) or Cellular data (erratic latency).
- Location Inference: By seeing exactly when you switch from home Wi-Fi to Cellular and back to work Wi-Fi, they can map your commute and daily routine.
- Social Graph: If two people consistently show "App Open" status at the same time, an attacker can infer they are talking to each other.
- Cross-Device Mapping: The attack is multiplied if you use desktop apps. Because encryption handles every device separately, your phone and your laptop generate independent delivery receipts. An attacker can overlay this data to see exactly when you shut your laptop and immediately switch to your phone, creating a high-fidelity timeline of your physical movements and habits.
The Invisible Resource Drain
You might think you’d notice someone spamming you to track your activity. You wouldn’t.
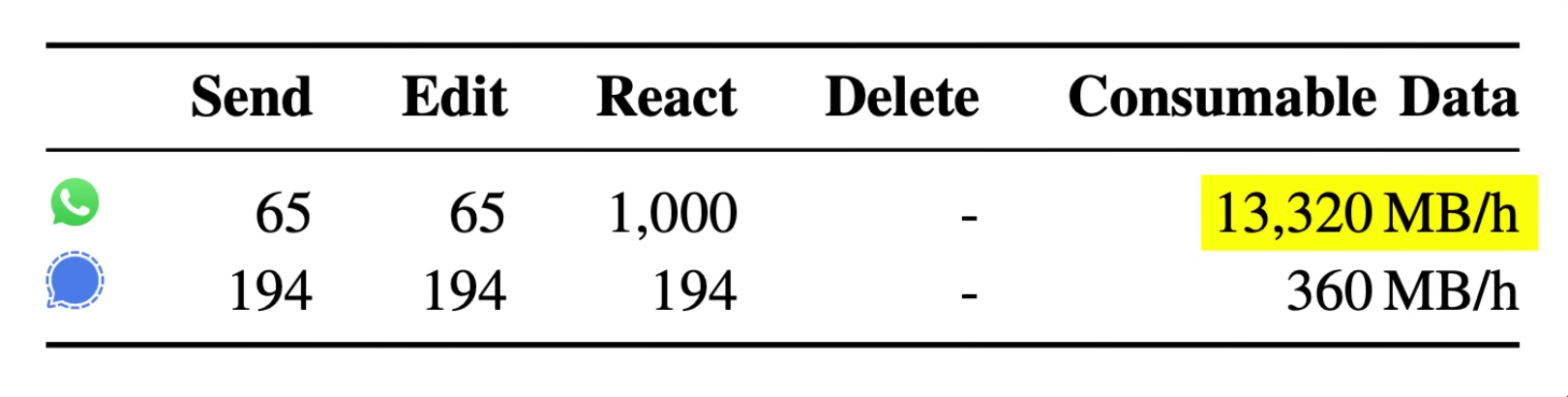
The exploit uses reactions (like a heart emoji or anything else) attached to messages that don’t even exist. Your phone receives the data, processes it, sends the receipt, and then silently discards it because there is no message to react to.
No notification. No vibration. You see NOTHING.
But your phone is working hard in the background. The researchers showed that a sustained attack can be devastating to your resources:
- Data Usage: It can burn through ~13 GB of data per hour.
- Battery Life: It can drain your battery by ~18% per hour, even while the phone is in your pocket.
If your phone suddenly gets hot and your data plan evaporates, you might not be scrolling too much. You might be getting mapped.
The "Big Tech" Implication
This is where we need to stop and think.
Remember, these researchers are outsiders. They are effectively standing on the street corner with a stopwatch, guessing what's happening inside your house by measuring how long it takes for the lights to flicker when they ring the doorbell.
If threat actors can retrieve this much granular detail simply from delivery receipt delays, imagine the amount of data Big Tech has on you.
Meta (WhatsApp) and the OS providers (Google/Apple) don't need to measure latency. They own the server, the application, the push notification system, and the operating system itself. If a clumsy timing attack can reveal your sleep schedule, device type, and location habits, the behavioral dossier sitting on Big Tech servers is likely beyond our comprehension.
"It's Not a Bug"
We often assume vulnerabilities are accidents. But look at the industry response when this was disclosed:
- WhatsApp: They marked the report as a "duplicate," ignored it for nearly a year, and closed the ticket without a fix.
- Signal: Did not respond to the researchers.
I’m just a simpleton when it comes to coding at these levels, but isn't the fix extremely simple? Add a random delay when sending the receipt. Or just let us turn the damn things off, the same way we do with Read Receipts.
The lack of action over the years begs the question: What if this isn't a bug, but a feature?
The lock on the door is strong (E2EE), but the walls are made of glass. Yikes. Who knows what else lies in plain sight? Three-letter agencies are sure happy about it.
Source: Careless Whisper Paper (University of Vienna / SBA Research)
